We also provide
Enterprise PKI
- Windows smart card logon
- Certificate-based authentication of mobile devices (SCEP, PKCS#12)
- Certificate-based 802.1X authentication (EAP-TLS)
- Certificate-based authentication against systems and web applications / services
- Electronic signing of documents, applications, and macros
keyon true-Xtender Suite for Enterprise PKI
- Web-based, multi-tenant registrar, and service APIs
- Third-party certificate management and automatic registration for public CAs
- Enforcement of guidelines and control of the entire certificate management
keyon true-Xtender Policy Module
The true-Xtender Policy Module extends the features of Enterprise PKI and allows a rule-based issuance and management of X.509 certificates. The certificate content can be considerably extended or modified. Here are some examples:
- The individual components of the subject distinguished name (DN) can be defined, taken from the original certificate application, or modified and extended by any rule.
- X.509 certificate extensions can be randomly removed, adjusted, enhanced, or added. Host specific extensions such as the RACF ID can also be managed with the true-Xtender Policy Module.
- Additional user or system attributes can be selected from a directory or database and integrated into the certificate.
keyon true-Xtender Registration Authority
keyon true-Xtender Registration Authority Web Application
The keyon true-Xtender Registration Authority Web Application enables the seamless integration of certificate management into the company’s internal processes and offers next to a browserbased GUI a web service interface for automated processes.
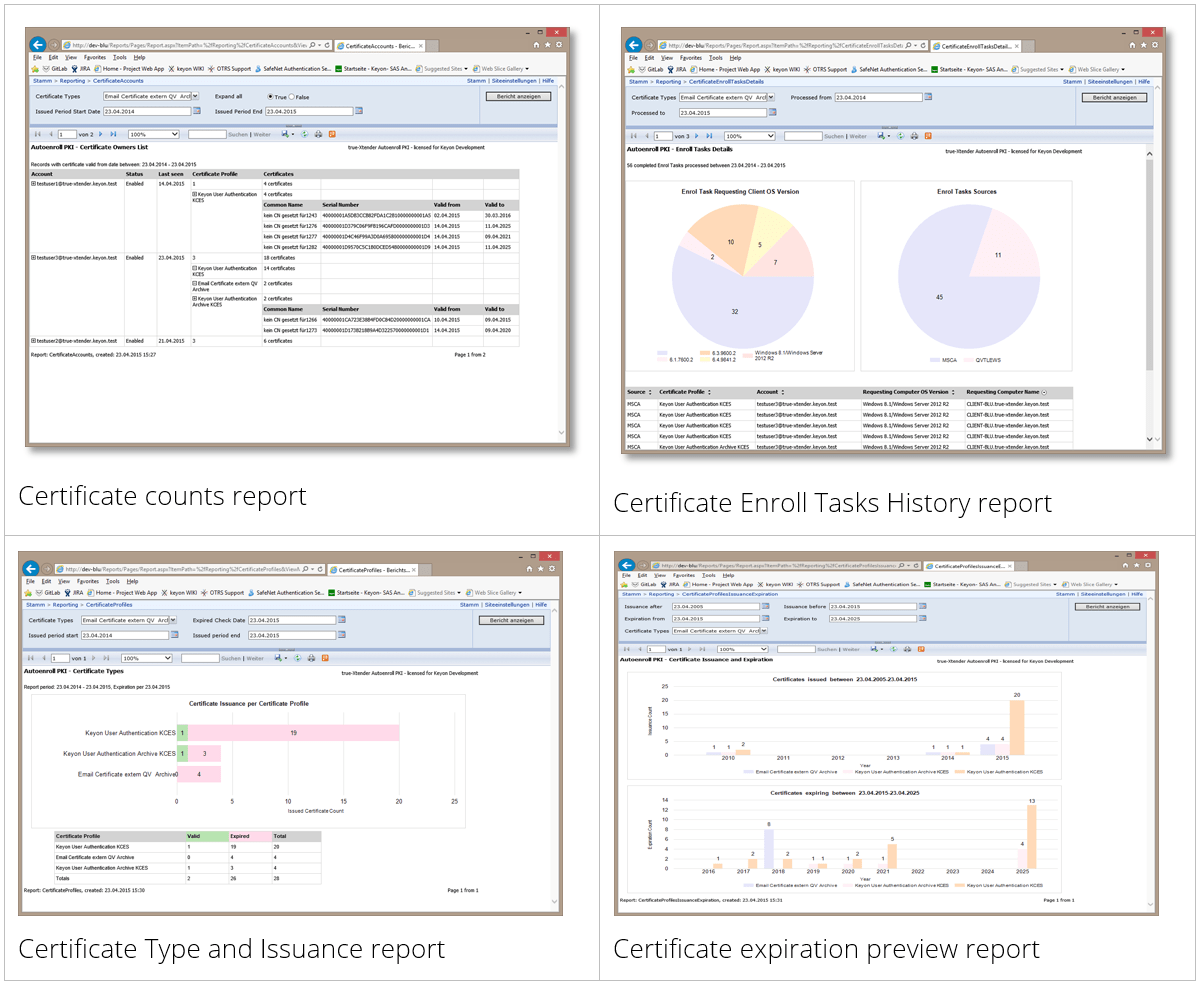
Company specific management processes can be implemented through metadata, which are additionally stored in the registration authority (RA) database. For example, certificates can be mapped to applications, individuals or groups, who will be notified in case of a renewal process, a revocation, or other activities. An extensive audit log stores every activity of the applicants and the administrators. The permissions for the individual features are controlled via Active Directory groups. The RA stores all data in a Microsoft SQL database. Evaluations and reports can be created using Microsoft SQL Server Reporting Services (SSRS) or Microsoft Power BI. The RA supports different workflows, which can be defined for each certificate type.The keyon true-Xtender Registration Authority Web Application provides the following features:
- simple and advanced search for certificates,
- issuing certificates based on PKCS#10 files,
- issuing key pairs and certificates as PKCS#12 files,
- delivering already issued certificates via different channels (e-mail, web-based download),
- safety-critical features can be mapped through a workflow management (four-eye-principle),
- revocation of certificates, and
- renewal of certificates.
The keyon true-Xtender Registration Authority Web Application is based on Microsoft IIS.
keyon true-Xtender Registration Authority ACME Service
The keyon true-Xtender Registration Authority ACME Service provides the ACME protocol as a standardized interface for the automated certificate management.
The RA-ACME Service is integrated into the RA database and its user interface. The RA-ACME Service is implemented as a proxy server architecture, which enables the use of ACME in separate network zones. Several ACME adapters act as a proxy between the enrollment clients and the RA, or the RA-ACME Service. The ACME adapters perform the validation of the domains. The adapters support the ACMEv2 protocol with HTTP validation (according to RFC 8555). Various certificate profiles are supported for different domains by using different endpoints in the service URL of the adapters. The adapters are available for Windows and Linux systems.
keyon true-Xtender Registration Authority Reminder Services Add-on
keyon true-Xtender Registration Authority Web CA Add-on
keyon true-Xtender Registration Authority Web Service Add-on
The keyon true-Xtender Registration Authority Web Service Add-on offers extensive REST and / or SOAP interfaces for the automated issuance and management of X.509 certificates. An enrollment client authenticates itself against the web service and receives based on the corresponding AD group membership and the role concept the appropriate permissions for the individual features:
- issuing certificates based on PKCS#10 files,
- issuing key pairs and certificates as PKCS#12,
- obtaining issued certificates,
- revocation of certificates, and
- renewal of certificates.
keyon true-Xtender Registration Authority DCOM Add-on
keyon true-Xtender Third-Party Certificate Manager Add-on
keyon true-Xtender AutoEnroll PKI Proxy
keyon true-Xtender AutoEnroll PKI
Furthermore, the Enterprise PKI auto-enrollment feature can be extended significantly with keyon true-Xtender TX-AE.
- Auto-enrollment of public certificates. Any public CA with a web service interface can be integrated.
- Auto-enrollment based renewal of certificates in the case of modifications of user or server attributes.
- Flexible lifecycle management of user and server certificates.
keyon true-Xtender PKI Services
keyon true-Xtender Auto-Revocation Service
The keyon true-Xtender Auto-Revocation Service is the counterpart of Microsoft’s auto-enrollment feature. The true-Xtender Auto-Revocation Service revokes a certificate as soon as its associated computer or user object is deleted in AD. It also revokes duplicate certificates, i.e. certificates of the same type issued to the same subject DN.
The threshold value of the number of certificates to be revoked can be configured to prevent unintentional revocation in case of AD structure changes (e.g. moving users to a different OU). All actions of the service are recorded in the Windows Application Event Log.
keyon true-Xtender Standalone Certificate Expiration Service
keyon true-Xtender CRL Management Service
keyon true-Xtender CRL Publication Service
The keyon true-Xtender CRL Publication Service publishes the certificate revocation list (CRL) immediately after the input of a so-called revocation request on the Microsoft CA. Furthermore, a blacklist is published in a regular interval (e.g. once a day) even if no new entry exists on the revocation list.
By using the SE-CP, the regular publication of revocation lists is omitted whereby no unnecessary rereading of an online responder is required. The revocation list is only reread when the list is updated due to a new revocation request.
The SE-CP is installed as Windows Service and is registered as a so-called exit module on the Microsoft CA. The publication interval and other application specific parameters can be configured in an XML file.
Keyon Coaching Resync Revocation Provider
Keyon Caching Resync Revocation Provider
The check against revocation takes place in the Windows CryptoAPI through installable revocation providers, whereby Microsoft provides a revocation provider by default that can detect the revocation details via OCSP and revocation lists.
When using CRLs through the standard Microsoft revocation provider, it cannot be assumed that the revocation of a certificate can be detected in a timely manner because the CRLs and the OCSP responses are cached due to various parameters.
The Keyon revocation provider make sure that CRLs and OCSP responses from a CA are reloaded after a configurable time instead of being read from the cache.
Example of us: When issuing temporary smart cards, the active smart card is suspended and temporarily listed on the CRL. In order for an employee to use his old smart card as soon as possible after returning the temporary smart card, the domain controller must use the latest CRL after the suspension.
The Keyon Caching Resync Revocation Provider is primarily used on domain controllers and Windows Servers where user certificates are checked against revocation.
Keyon Fallback and BCM Revocation Provider
By using the Keyon Fallback and BCM Revocation Provider, a Windows login using a smart card can be guaranteed even after a longer total failure of a PKI.
If a domain controller can’t check its own certificate at the start with a valid CRL or OCSP request, it then deactivates the feature for the smart card logon.
If none of the installed revocation providers can retrieve valid revocation details, then the Keyon Fallback and BCM Revocation Provider return the status “not revoked” for the domain controller certificate. The Keyon Fallback and BCM Revocation Provider is primarily used on domain controllers and Windows clients.
Keyon Credential Provider
The Keyon Credential Provider allows the enforcement of the smart card logon without randomizing the Active Directory (AD) password of an employee. This allows compatibility with applications that check user names and passwords against AD and do not support Kerberos or certificate-based authentication.
The Keyon Credential Provider allows the username /password logon only for local administrators and for members of defined AD groups. In addition, so-called “deny password logon” AD groups can be defined, which overrides AD groups for which smart card logon is not enforced.
If the Keyon Credential Provider cannot determine whether a user is local admin or member of a defined AD group, the login with username and password is not possible. The Keyon Credential Provider caches group memberships of users to support the offline logon scenario.
A second smart card credential provider wrapper allows to change the AD password, if required by policy, when the user tries to login with a smart card. This guarantees that password change policies can be enforced even for users that are only allowed to interactively login with a smart card.
The Keyon Credential Provider supports Windows 7 and Windows 10. The configuration can be set by group policies.
Keyon Certificate Progator
The Microsoft certificate propagation service (CertPropSvc) imports the certificates into the user certificate store when the smart card is inserted and during the logon/unlock process.
The Microsoft certificate propagation service (CertPropSvc) runs as a standard for all smart cards available on a system, which means that the certificates of other users are also propagated into the certificate store of the currently logged in user. These certificates are then displayed in selection dialogs.
Keyon Certificate Propagator Service functionality
The Keyon Certificate Propagator replaces the Microsoft certificate propagation service (CertPropSvc) and imports only the certificates of the currently logged in user, which are to be imported according to the configuration.
The Keyon Certificate Propagator has an architecture that allows to extend the functionality at various events (smart card plugged, smart card removed) through plug-ins in the form of DLLs. This architecture allow applications or scripts to be started on an event such as the pending certificate renewal.
When the CE-PR is started, the following actions are performed:
- The certificates of all smart cards currently available on the system are identified.
- Smart card certificates that have been assigned to a smart card CSP / KSP but are not found on any of the smart cards used are deleted from the user’s certificate store.
- The certificates on the inserted smart card are identified.
- Smart card certificates that have the same user ID but do not exist on any of the inserted smart cards are deleted from the user’s certificate store.
While the application is running, the following actions are performed when a smart card is removed:
- If the certificates on the remote smart card belong to the logged in Windows user (UPN in authentication certificate = UPN of the Windows user), no actions are taken and no certificates are deleted.
- If the certificates on the remote smart card do not belong to the logged in Windows user, then the certificates are deleted from the user’s certificate store.
Vendors & Certifications
Pioneering products and solutions from the world’s leading vendors


Keyon
Keyon AG is a leading provider of solutions and services in the areas of IT security and customer-specific software development. The company, which has been operating since 1999, has implemented first-class references and a large number of strategic projects for the federal government and our customers in the areas of finance, insurance, trade, industry and telecommunications. They support their customers in all phases of the project and like to be measured by the success of their work.
We also provide
The following services might also be of interest to you
